Introducing File Signature Verifier
PGP cryptographic file signatures are popular amongst open source projects of all types. Sometimes publishers will opt to release them over simple file hashes.
They'll appear next to download links in the form of a .sig or .asc file, but what are they good for?
There are several very good theoretical explanations out there so let's look at the practical side of things.
- You download something made by a source you trust
- You want to make sure that this file was actually released by the trusted source
- You want to make sure nothing and nobody has tampered with it on the server or en-route to you.
Basically you want to make sure the file is intact and authentic.
That's what signatures are good for.
Signatures do more than hashes when used appropriately since hashes only validate integrity.
If an attacker gains control over a software release page they can easily swap the genuine releases for their own, modified ones and change the hashes on the page as well without you noticing. A signature however, in addition to verifying the integrity will also authenticate the source of the file. Assuming the publisher has kept their private key secure and you have a trusted copy of their public key you will be able to verify whether a release you've downloaded is genuine or not.
The single most important factor from your perspective is to get a trusted copy of the publisher's public key, save it, and reuse it for future verifications.
It's a bit less secure if you always download the public key from a project's page.
An attacker can't produce a signature that will validate his tampered copy of a file with the genuine public key of the project (without gaining access to the publisher's private key) but they could theoretically sign all of the releases on a page with their own fake private key and then set the download links to their fake public key, though this is very unlikely to go unnoticed.
Another thing worth mentioning is the OpenPGP key server pool, a network of servers which hold public keys that can be downloaded with the appropriate client software based on the key id number.
You can be reasonably sure about the authenticity of a publisher's key if you confirm it's ID from several sources (via google search for example) and then fetch it from the key server based on said id. Most public projects using signatures will have uploaded their public key to the pool.
So how can you verify file signatures?
This is where our new tool comes in:
File Signature Verifier
Verify files cryptographically signed with PGP/GnuPG. Supports fetching keys from key servers.
Using it is pretty easy. You can either drag and drop all the ingredients (public key, signature and file to verify) at once like so:
Then just press the verify button:
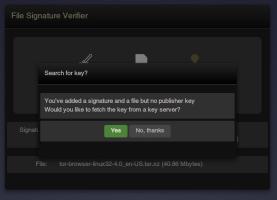
Or if you don't add the public key you can fetch it from a server:
The tool uses the OpenPGP key server pool by default. The "subset" pool excludes older servers that don't support JavaScript clients.
The key id is auto-filled from the signature. This is where you would make sure that the id really belongs to your trusted source.
Sometimes publishers will only give their key's short id which is the final 32bits (or 8 characters not including the 0x prefix) of the full id.
You can fetch keys from the keyserver based on the short id as well as the full one.
That's it!
If don't want to/can't drag and drop you can also browse for files by simply clicking/tapping on the icons.
The key icon will give you a choice between fetching from a server and browsing for a file.
Check it out and let us know what you'd like to see next!